This is a response post to the article “Understanding The DAO Hack for Journalists“
I’m surprised of how much errors are in this piece written for journalists.
I understand that this is a complicated ongoing topic, but its important to get the information right here. So i will point out just a few things which are definitely wrong:
Correcting the article
At the time, more than 50 project proposals were waiting for The DAO’s token holders to vote on them.
Thats not really true, no proposal was whitelisted by the curators, so DTH could not vote on anything, except informal proposals going to the DAO itself: One can see all the (past) proposals here: http://vote.slock.it
Several people made attempts to split The DAO to prevent more ether from being taken, but they couldn’t get the votes necessary in such a short time.
Thats also not true, the splitDAO proposals where purely from people who wanted to solo split, means taking their own money out – most of them succeeded. Because of the attack a few additional people joined these solo splits and have now to figure out how to agree to the other people in the split to disperse the money in these child DAOs.
Even the attackers split (59), was NOT his own, he simply drained the ether into a DAO, where he is not the curator himself! The attacker DAO can be found here.
There are things the Ethereum Foundation could do that may be able to nullify the ether in this DAO. That’s where things get complicated.
The foundation itself has no involvement in the DAO. Concerning power, it has technically as much power as everybody in the ecosystem.
With the latest release of geth 1.4.8 it allows the community to choose a Soft Fork or to continue as usual. As it currently stands the miner community has voted FOR a soft fork.
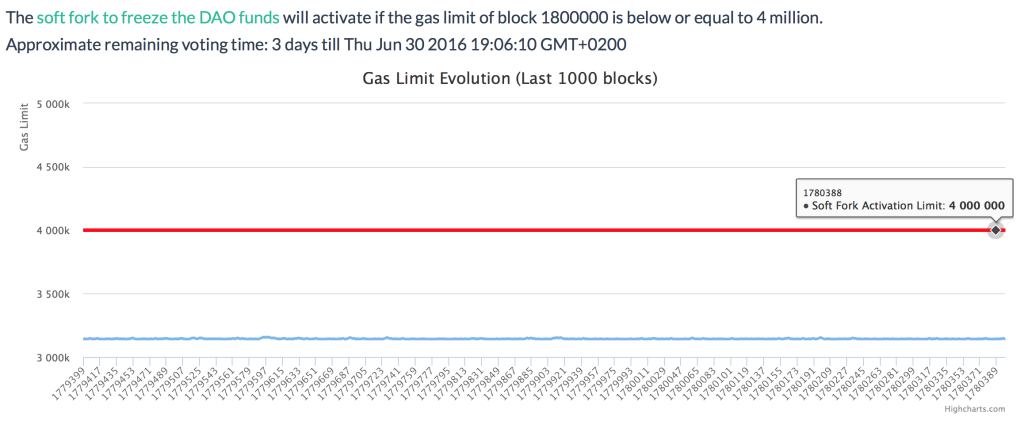
]6 If the blue line is below the red line on thursday the 30th the soft fork will enable
Because the designers didn’t expect this much money, all the ether was in a single address (bad idea), and we believe the attacker stopped voluntarily after hearing about the fork proposal (see below). In fact, that attack, or another similar one, could continue at any time.
Thats also not true (anymore). Due to the white hat attack, which secured 7.2M ether in a child DAO with all, but one unknown actors the rest of the money is safe from 20k unknown potential attackers.
What does the Soft Fork do?
The Soft Fork does not freeze the funds forever. The SF still allows two addresses: the curators/guardians and the token holder of the white hat DAO to act. Which allows to withdraw the 7.2M ether into a redistribution fund, so DTH can get at least this part back, after the creation phase ended on this DAO.
This SF would also allow to counter attack the DarkDAO(s) by buying into the DarkDAO. But this would need to be voted on by the DTH. If the buy-in is successful the DTH can split from the attacker, withdrawing all the ether in another DAO. The attacker can’t follow due to the SF. After this new child-child DAOs creation period, these funds could be recovered as well.
Concerning the 4 other DarkDaos (one with 269.82 Ether, one with 859.19 Ether, one with 11,605.31 Ether and one with 268,320.82 Ether). Most of them are infiltrated and therefore the curator/white hat address can use the same way to get the ether out as in the other counter-attacks. The SF here will ensure that no attacker, but the curators/white hat can withdraw any ether from these DAOs.
What about a Hard Fork?
A hard fork would basically put a rule in place where on a specific block either the DAO code gets replaced with a refund contract, and/or the balances of all DAO’s will be moved into a refund contract.
This would solve the problem the fastest, but would introduce a cryptographic gap, as there is no transaction which ever created that transfer of ether.
From a purist point of view this is bad as it breaks the cryptographic proofs at this point in the chain. From a consensus point of view it doesn’t matter, as long as all nodes agree to this step.
In any case whatever is the way forward with this Soft Fork in place we have now 2 options:
- The DAO attacks the attacker and all attacker DAOs funds can be refunded, but it is a slow and cumbersome process, which can take up to 30-70 days
- The network hard forks to re-gain the ether stolen by the attacker, which he can’t get to anyway due to the soft fork.
I hope this blog post sheds a bit more light on the current situation and the ways forward.